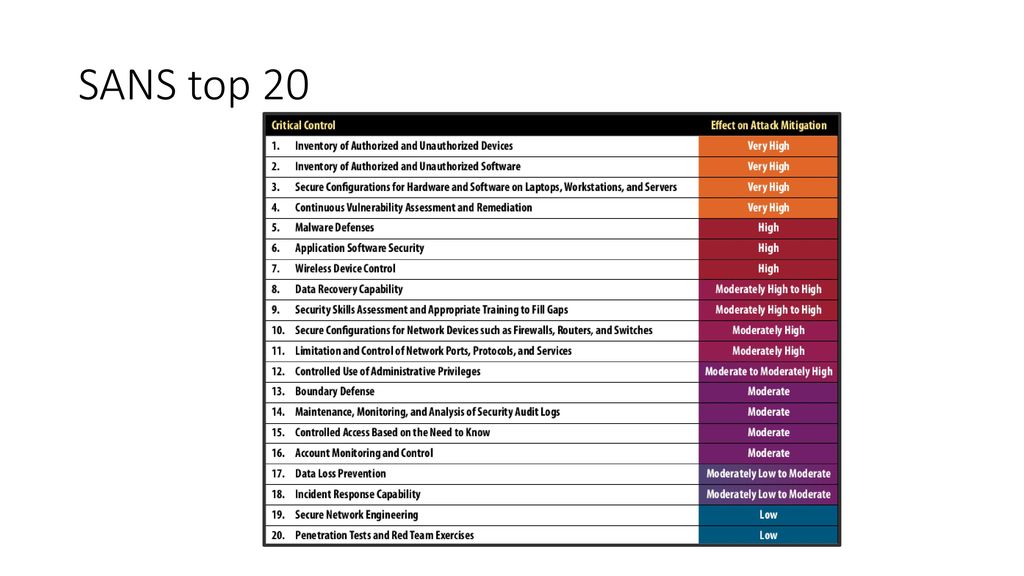
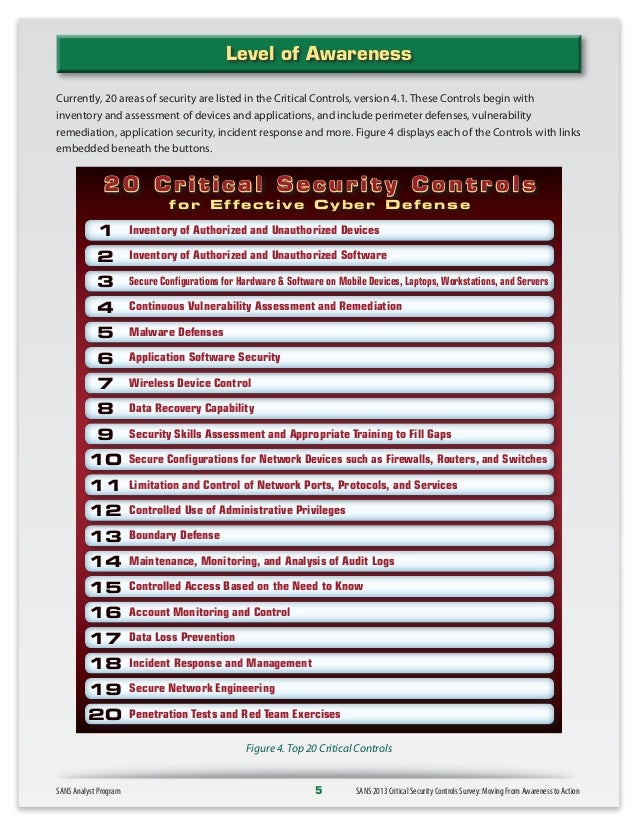
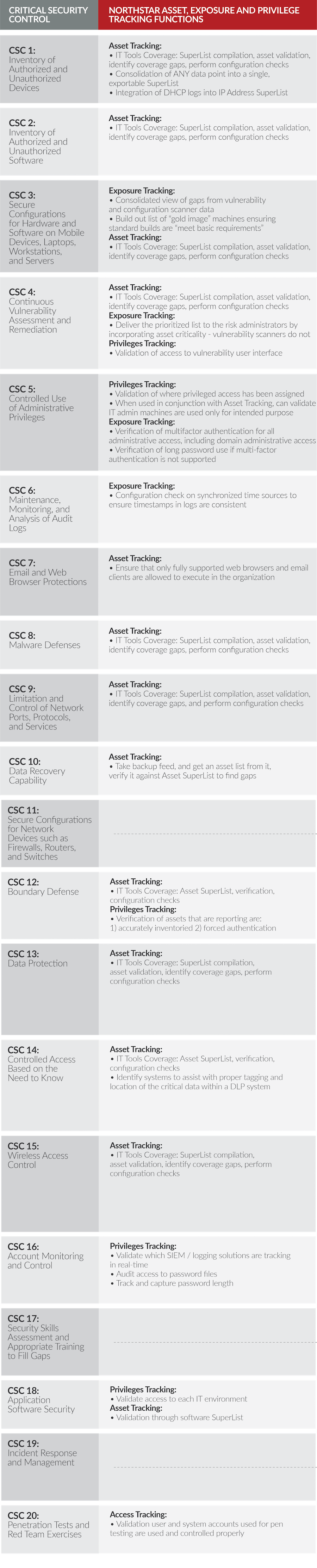
Michael Fisher Twitter પર: "What are the top 20 controls for a healthy network #Security posture? {Infographic} #CyberSecurity #infosec #education #DevOps #Malware #databreach #Pentesting #IRP… https://t.co/Jw0Wr96CSm"
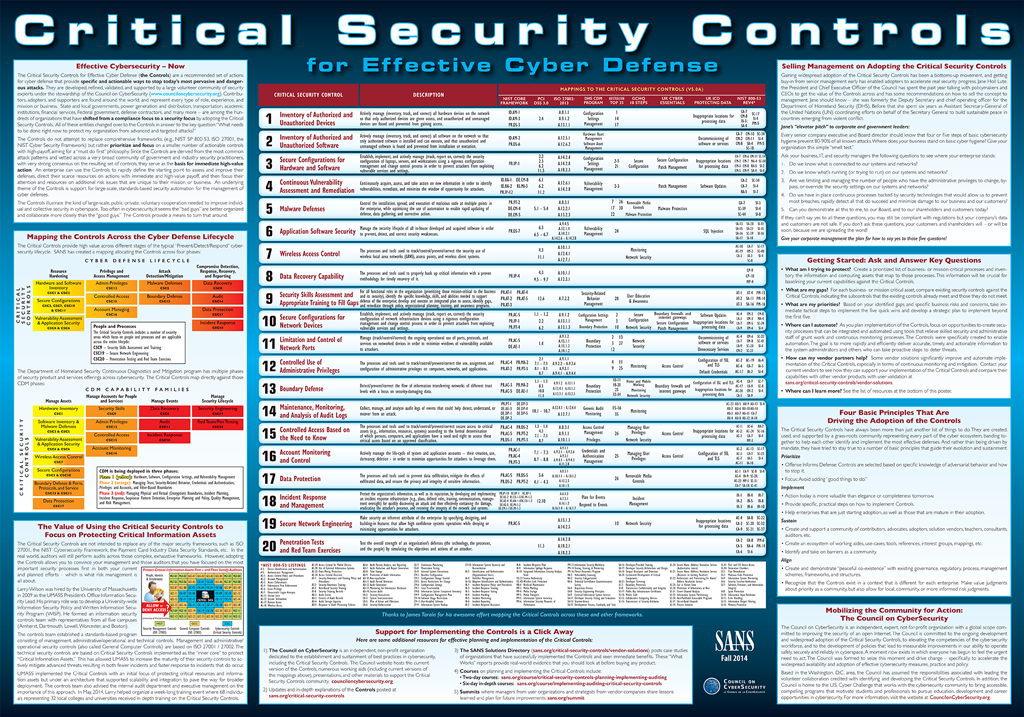
SANS Institute on Twitter: "20 CRITICAL SECURITY CONTROLS | POSTER: Set of actions for cyber defense. DL > PDF (2pgs) - http://t.co/YZGlCbuXmd http://t.co/moeIozrqu0"